Your Annual Security Training Isn't Working (Here's What Actually Does)
We’ve all been there. It’s that time of year again. An email lands in your inbox with a subject line that makes your heart sink: “Mandatory Security Awareness Training Due by Friday.”
You click through a series of slides featuring cartoonish hackers in hoodies, answer some multiple-choice questions about password strength, and check the box. Done. Compliant. Safe.
Except you’re not safe at all.
Here’s the uncomfortable truth we need to talk about: your annual security training isn’t working. Not because the content is wrong (though it often is), but because the entire approach is fundamentally broken. We’ve turned security awareness into a compliance checkbox, and we’re shocked when employees keep clicking phishing links the week after completing their training.
The security training industrial complex has convinced us that sitting through an hour-long module once a year will somehow transform our teams into human firewalls. It won’t. And deep down, we all know it.
So why do we keep doing it this way?
The Compliance Trap: How We Got Here
Annual security training exists for one primary reason: someone decided it needed to exist. Maybe it was an insurance requirement. Maybe it was a checkbox on a compliance framework. Maybe a well-meaning IT director saw one too many successful phishing attacks and thought training would solve everything.
Whatever the origin, we’ve created a system where the goal isn’t learning or behavior change. The goal is completion rates.
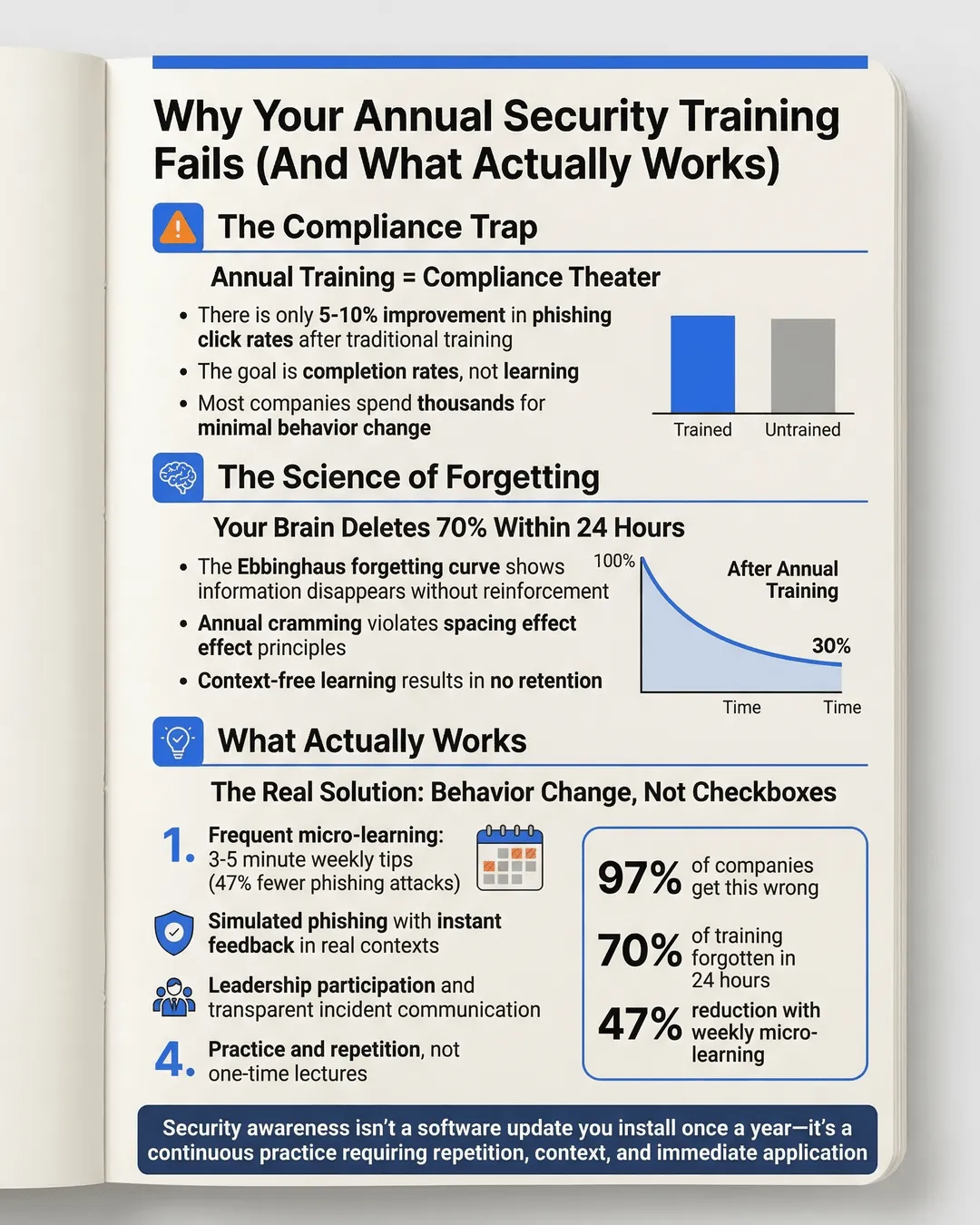
Research from KnowBe4 shows that employees who complete traditional annual security training have only a 5-10% better phishing click rate than those who receive no training at all.¹ That’s not a typo. We’re spending thousands of dollars and hundreds of employee hours for a marginal improvement that disappears within weeks.
The problem isn’t that employees don’t care about security. The problem is that we’re asking them to absorb a year’s worth of security concepts in a single sitting, apply them to situations they haven’t encountered yet, and remember everything when a real threat appears six months later.
That’s not how human brains work.
Traditional annual security training treats learning like a software update. Download the information, install it once, and you’re good for another year. But security awareness isn’t a one-time installation. It’s a continuous practice that requires repetition, context, and immediate application.
Key Takeaways
- Annual security training achieves compliance but rarely changes behavior, with completion rates mattering more than actual learning outcomes.
- Human brains need repetition and context to form habits, which single yearly training sessions cannot provide.
- Effective security culture requires frequent, bite-sized learning moments integrated into daily workflows.
- Simulated phishing exercises and real-time feedback create lasting behavior change better than passive training modules.
- Leadership participation and transparent communication about security incidents build trust and accountability across organizations.
Why Your Brain Forgets Everything You Learned in That Training
Let’s get into the science of why annual training fails.
The forgetting curve, discovered by psychologist Hermann Ebbinghaus, shows that we forget approximately 70% of new information within 24 hours unless we actively reinforce it.² When you complete that annual security training module, most of what you learned is gone before you finish your morning coffee the next day.
But it gets worse. The spacing effect in learning tells us that information reviewed at spaced intervals is retained far better than information crammed into a single session.³ Yet we keep cramming an entire year’s worth of security concepts into one hour-long module.
Think about how you learned to drive. You didn’t watch a video about driving once, take a quiz, and then get behind the wheel a year later. You practiced repeatedly, received immediate feedback, and gradually built muscle memory through consistent repetition.
Security awareness works the same way. Recognizing phishing emails, creating strong passwords, and reporting suspicious activity are skills that require practice and reinforcement, not annual lectures.
The other problem with annual training is context collapse. When you’re sitting through a generic module about password security, you’re not actively creating a password. The lesson has no immediate application, so your brain files it under “might need this someday” rather than “critical information for right now.”
Compare that to a quick security tip that pops up exactly when you’re about to click a suspicious link. The context makes the lesson stick because you’re applying it immediately.
What Actually Changes Security Behavior
We’ve spent enough time on what doesn’t work. Let’s talk about what does.
Organizations that have successfully built strong security cultures share common characteristics that have nothing to do with annual training completion rates. They’ve shifted from compliance-focused education to behavior-focused practice.
Frequent micro-learning beats annual marathons. Instead of one hour-long session per year, effective programs deliver 3-5 minute security tips throughout the year. Short, focused lessons on single topics create better retention and allow employees to immediately apply what they learned. Security awareness platform ThreatLocker found that companies using weekly micro-learning reduced successful phishing attacks by 47% compared to those using only annual training.⁴
Simulated phishing exercises create real consequences. Nothing teaches phishing recognition better than clicking a simulated phishing link and immediately seeing a learning moment. These exercises work because they provide instant feedback in the exact context where the behavior matters. The key is making them educational rather than punitive. When employees who click simulated phishing links receive immediate, helpful guidance rather than shame, they’re far more likely to report real threats in the future.
Security conversations replace security lectures. The best security programs create ongoing dialogues, not one-way information dumps. Regular security discussions in team meetings, Slack channels dedicated to security tips, and open conversations about near-misses normalize security as part of daily work rather than an annual obligation. According to a study by Stanford University, employees who regularly discuss security with colleagues are 3.5 times more likely to report suspicious emails.⁵
Leadership models security behavior visibly. When the CEO talks openly about almost falling for a phishing email, it creates psychological safety for everyone else to admit their mistakes and ask questions. Security can’t be something that only IT cares about. It needs to be modeled from the top down.
Real incidents become learning opportunities. Rather than hiding security incidents out of embarrassment, mature security cultures use them as case studies. Sharing what happened, how it was caught, and what everyone learned transforms incidents from failures into valuable teaching moments.
Building a Security Culture (Not Just Checking Compliance Boxes)
Here’s what a functional security awareness program looks like for small and medium-sized businesses.
Month-round engagement. Send a brief security tip every week or two. Mix formats: short videos, infographics, quick quizzes, real-world examples from recent news. Keep it varied and keep it coming. The goal is to make security awareness as routine as checking email.
Contextual reminders. Integrate security prompts into existing workflows. When someone is about to share a document externally, a quick reminder about data classification helps. When setting a new password, a tip about password managers appears at the right moment.
Ongoing phishing simulations. Run simulated phishing exercises monthly or quarterly, varying the sophistication and tactics. Track trends over time rather than punishing individual clicks. Celebrate teams that improve their detection rates.
Security champions program. Identify interested employees across different departments and give them slightly deeper security training. These champions become resources for their teams, answer questions, and help spread security awareness organically through the organization.
Transparent reporting. Share security metrics openly. Let everyone know how many simulated phishing emails were caught versus clicked. Show trends over time. Celebrate improvements and discuss challenges honestly.
Make it easy to do the right thing. Provide password managers. Enable two-factor authentication by default. Create simple reporting mechanisms for suspicious activity. The easier you make secure behavior, the more likely people are to practice it.
None of this means you should eliminate annual training entirely. Compliance requirements exist for good reasons, and you still need to check those boxes. But compliance training should be the baseline, not the entire program.
The goal isn’t to turn every employee into a security expert. The goal is to create an environment where security-conscious behavior becomes habitual, where people feel comfortable asking questions, and where reporting potential threats is as natural as reporting a printer jam.
Conclusion
Your annual security training isn’t changing behavior because behavior change doesn’t happen in annual installments. It happens through consistent practice, immediate feedback, and cultural reinforcement.
The uncomfortable truth is that we’ve been doing security training the easy way, not the effective way. It’s easier to buy an off-the-shelf training module, assign it once a year, and call it done. It’s harder to build ongoing engagement, create regular touchpoints, and invest in cultural change.
But here’s the thing about security: half-measures don’t work. You can’t be sort of secure or mostly protected. Either your team has developed the habits and awareness to recognize threats, or they haven’t.
We’ve been treating annual security training like a vaccine—one shot provides immunity. It’s actually more like exercise. You don’t work out once a year and expect to stay fit. You build a routine, show up consistently, and make it part of your lifestyle.
The same applies to security awareness. Stop checking boxes. Start building habits. Your future self (and your cyber insurance provider) will thank you.
Citations
- KnowBe4, “Phishing By Industry Benchmarking Report,” 2024.
- Ebbinghaus, H., “Memory: A Contribution to Experimental Psychology,” 1885 (replicated in modern studies through 2024).
- Cepeda, N.J., et al., “Spacing Effects in Learning: A Temporal Ridgeline of Optimal Retention,” 2008.
- ThreatLocker, “Security Awareness Training Effectiveness Study,” 2024.
- Stanford University, “Organizational Security Culture and Employee Reporting Behavior,” 2023.