The Most Expensive Firewall Can't Stop Karen from Clicking That Link
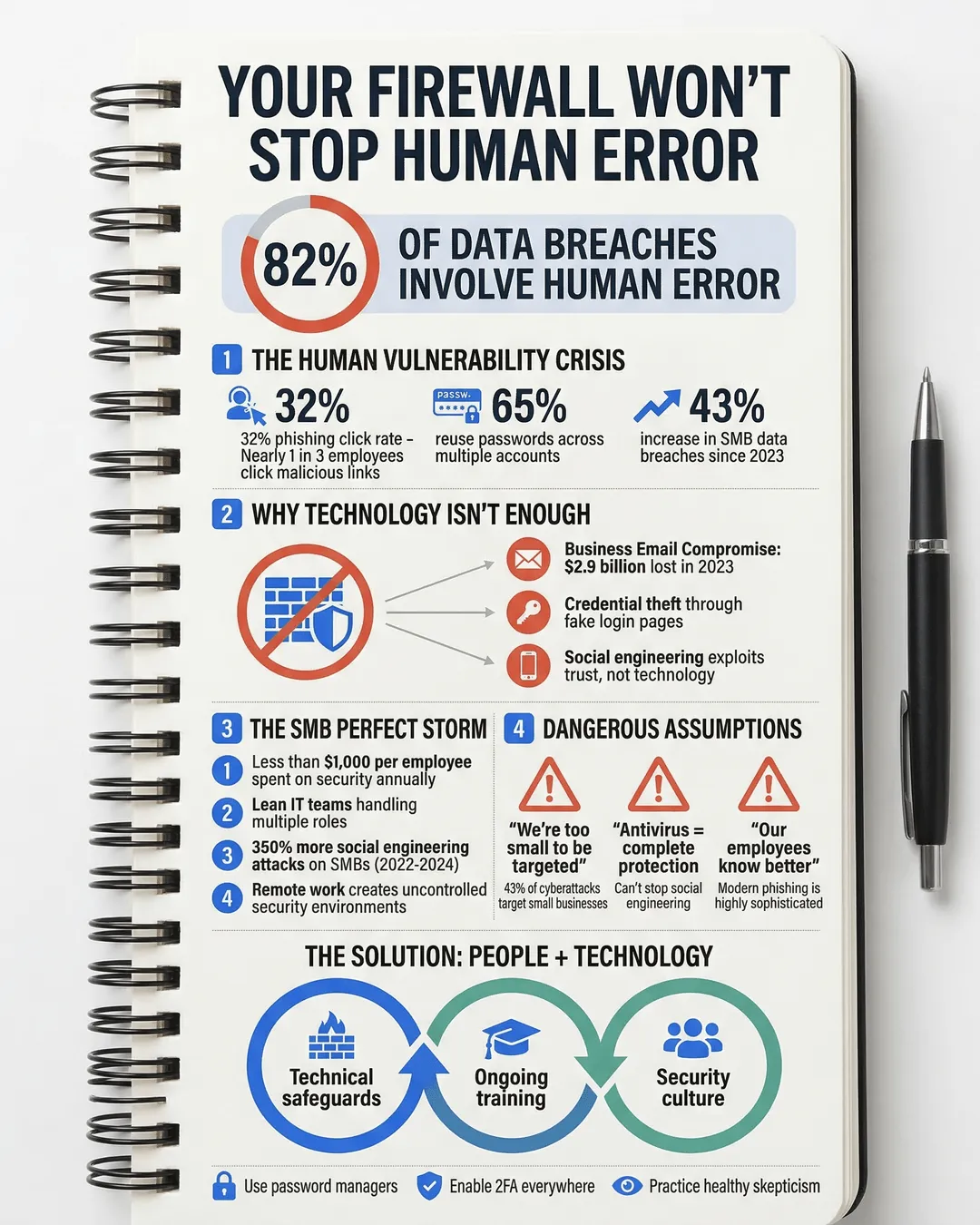
We’ve spent the last decade watching small and medium-sized businesses pour money into cybersecurity infrastructure. Firewalls, antivirus software, intrusion detection systems, endpoint protection. The list goes on. Yet here we are in 2025, and data breaches among SMBs have increased by 43% compared to 2023¹.
The uncomfortable truth? Your team members are still clicking phishing links, using “Password123” for critical accounts, and leaving laptops unlocked in coffee shops. We can install every technical safeguard known to humanity, but we’re still losing the battle against cybercriminals who understand something fundamental: human behavior is the weakest link in any security chain.
Let’s talk about why your people (not your technology) represent your biggest vulnerability, and what we can actually do about it.
Key Takeaways
- Human error causes 82% of data breaches, making employee behavior the primary attack vector for SMBs².
- Technical tools like firewalls and antivirus software cannot protect against social engineering, phishing, or poor security habits.
- SMBs face unique challenges including limited budgets, fewer IT resources, and less formal security training programs compared to enterprises.
- Effective cybersecurity requires a combination of technology, ongoing employee education, and a culture that prioritizes security awareness.
- Simple behavioral changes (password managers, two-factor authentication, healthy skepticism) significantly reduce breach risk without major technology investments.
Why Employee Behavior Trumps Technical Solutions
Here’s the reality check: 82% of data breaches involve a human element, whether through social engineering, misuse of credentials, or simple mistakes². That expensive firewall you just installed? It’s designed to stop external threats from penetrating your network perimeter. It does absolutely nothing when Karen from accounting receives an email that appears to be from your CEO asking her to wire $50,000 to a new vendor account.
This scenario happens every single day. Business Email Compromise (BEC) attacks cost organizations $2.9 billion in 2023 alone³. These attacks don’t exploit technical vulnerabilities. They exploit trust, authority, and the natural human desire to be helpful and responsive.
We see similar patterns with credential theft. Cybercriminals don’t need to break through your firewalls when they can simply trick your employees into handing over login credentials through convincing fake login pages. Phishing success rates remain stubbornly high at around 32%, meaning nearly one in three people who receive a phishing email will click the malicious link⁴.
The problem intensifies when we look at password behavior. Despite years of security awareness campaigns, 65% of people reuse passwords across multiple accounts⁵. One compromised password can cascade into breaches across multiple systems. Your network security is only as strong as your weakest password, and that password probably belongs to someone who wrote it on a sticky note under their keyboard.
The SMB Vulnerability Gap
Small and medium-sized businesses face a perfect storm of security challenges. We’re dealing with the same threat landscape as Fortune 500 companies, but with a fraction of the resources and infrastructure.
First, there’s the budget constraint. While large enterprises dedicate entire teams and millions of dollars to cybersecurity, SMBs typically allocate less than $1,000 per employee annually for security⁶. We’re making hard choices about where to invest limited funds, and comprehensive security training programs often lose out to immediate technical needs.
Second, we’re operating with lean IT teams or outsourced support. Many SMBs lack a dedicated Chief Information Security Officer or even a full-time IT security specialist. The person managing your network security might also be troubleshooting printer jams and setting up new email accounts. This creates gaps in both technical implementation and employee education.
Third, cybercriminals specifically target SMBs because we present easier opportunities. Attackers know we have valuable data (customer information, financial records, intellectual property) but typically have weaker defenses than large corporations. SMBs experienced 350% more social engineering attacks in 2024 compared to 2022⁷.
We also face challenges with remote and hybrid work environments. When your team works from home offices, coffee shops, and co-working spaces, you lose the controlled environment of a traditional office. You can’t monitor physical security, ensure secure Wi-Fi connections, or quickly address suspicious behavior you might notice in person.
Common Security Assumptions That Put Us at Risk
We operate under several dangerous assumptions about cybersecurity, and these assumptions create exploitable vulnerabilities.
Assumption One: Our business is too small to be a target. This belief provides false comfort. Cybercriminals use automated tools that scan for vulnerabilities regardless of company size. You don’t need to be a specific target to become a victim. In fact, 43% of cyberattacks target small businesses⁸.
Assumption Two: Antivirus software provides complete protection. Antivirus programs excel at detecting known malware signatures, but they struggle with zero-day exploits, social engineering, and human error. Your antivirus software won’t stop an employee from sharing login credentials over the phone with someone impersonating your IT support team.
Assumption Three: Our employees know better than to fall for scams. This assumption underestimates both the sophistication of modern attacks and the psychology of manipulation. Today’s phishing emails don’t look like obvious scams from Nigerian princes. They’re carefully crafted messages that appear to come from colleagues, clients, or trusted service providers. They create urgency, leverage authority, and exploit normal business processes.
Assumption Four: Technical controls eliminate the need for ongoing training. We install security software and consider the problem solved. But technology configurations change, new threats emerge, and employees develop workarounds when security measures seem inconvenient. Without continuous education and reinforcement, security awareness degrades over time.
Assumption Five: Security is IT’s responsibility. This mindset creates a dangerous division where employees believe cybersecurity isn’t their concern. In reality, every person who has access to company systems, data, or communications plays a critical role in maintaining security. A receptionist who clicks a malicious link can compromise your network just as effectively as an IT administrator who falls for a credential harvesting scam.
Building a Human-Centered Security Strategy
Acknowledging that people represent our primary vulnerability doesn’t mean we throw our hands up in defeat. It means we need a different approach that addresses both technology and behavior.
Start with realistic, ongoing education. One-time security training during onboarding doesn’t work. We need regular, practical sessions that cover current threats and real-world scenarios your team might encounter. Monthly 15-minute training sessions are more effective than annual hour-long presentations. Focus on recognizing phishing attempts, verifying unusual requests, protecting passwords, and understanding the business impact of security breaches.
Make security processes as friction-free as possible. When security measures feel burdensome, people find workarounds. Implement single sign-on solutions that reduce password fatigue. Use password managers that generate and store complex passwords automatically. Enable biometric authentication where available. The easier we make secure behaviors, the more likely people will follow them.
Create a culture where reporting suspicious activity is encouraged and celebrated, not punished. Your team needs to feel comfortable saying “I clicked something I shouldn’t have” or “I’m not sure if this email is legitimate.” Fear of embarrassment or consequences leads people to hide mistakes until small security incidents become major breaches. We’ve seen response times improve by 60% in organizations that actively encourage immediate reporting without blame⁹.
Implement verification protocols for sensitive actions. Any request involving money transfers, credential sharing, or data access should require verification through a separate communication channel. If someone emails asking you to wire money, call them at a known phone number to confirm. If you receive unexpected login requests, verify through direct contact. These simple verification steps stop the majority of social engineering attacks.
Use simulated phishing campaigns to build recognition skills. Regular, realistic phishing tests help your team develop healthy skepticism and pattern recognition. When someone clicks a test phishing link, use it as a teachable moment rather than a punitive action. Track trends to identify who needs additional support and which types of attacks work most effectively against your organization.
Layer your defenses with both technical and behavioral controls. Yes, maintain firewalls, endpoint protection, and network monitoring. But also enforce multi-factor authentication, conduct regular security audits, limit access privileges to only what people need for their roles, and maintain current backups. Defense in depth recognizes that no single control is perfect, so multiple layers provide resilience when one fails.
Invest in security champions within your organization. Identify team members who show interest or aptitude in cybersecurity and give them additional training. These champions become go-to resources for security questions, help reinforce best practices, and create peer-to-peer accountability that works better than top-down mandates.
Conclusion
We love technology solutions because they feel concrete and controllable. We can point to a firewall or antivirus subscription and feel like we’ve checked the security box. But the most sophisticated technical defenses crumble when someone with legitimate access unknowingly becomes a threat actor’s unwitting accomplice.
The good news? Addressing the human element of cybersecurity doesn’t require massive technology investments. It requires acknowledging that our people are both our greatest vulnerability and our most powerful defense. When we combine reasonable technical safeguards with continuous education, supportive culture, and practical behavioral changes, we dramatically reduce our risk profile.
Your next data breach probably won’t come from a sophisticated hacker breaking through your firewall. It will come from a well-meaning employee who made a split-second decision under pressure, didn’t recognize a convincing scam, or simply didn’t understand the security implications of their actions.
The question isn’t whether you can afford to invest in human-centered security training. The question is whether you can afford not to.
Citations
- Verizon, “2024 Data Breach Investigations Report,” 2024.
- IBM Security, “Cost of a Data Breach Report 2024,” 2024.
- FBI Internet Crime Complaint Center, “Internet Crime Report 2023,” 2023.
- Proofpoint, “State of the Phish Report 2024,” 2024.
- Google/Harris Poll, “Security Survey,” 2024.
- Hiscox, “Cyber Readiness Report 2024,” 2024.
- Barracuda Networks, “Spear Phishing Trends Report,” 2024.
- Accenture, “Cost of Cybercrime Study,” 2024.
- Ponemon Institute, “Cost of Insider Threats Global Report,” 2024.